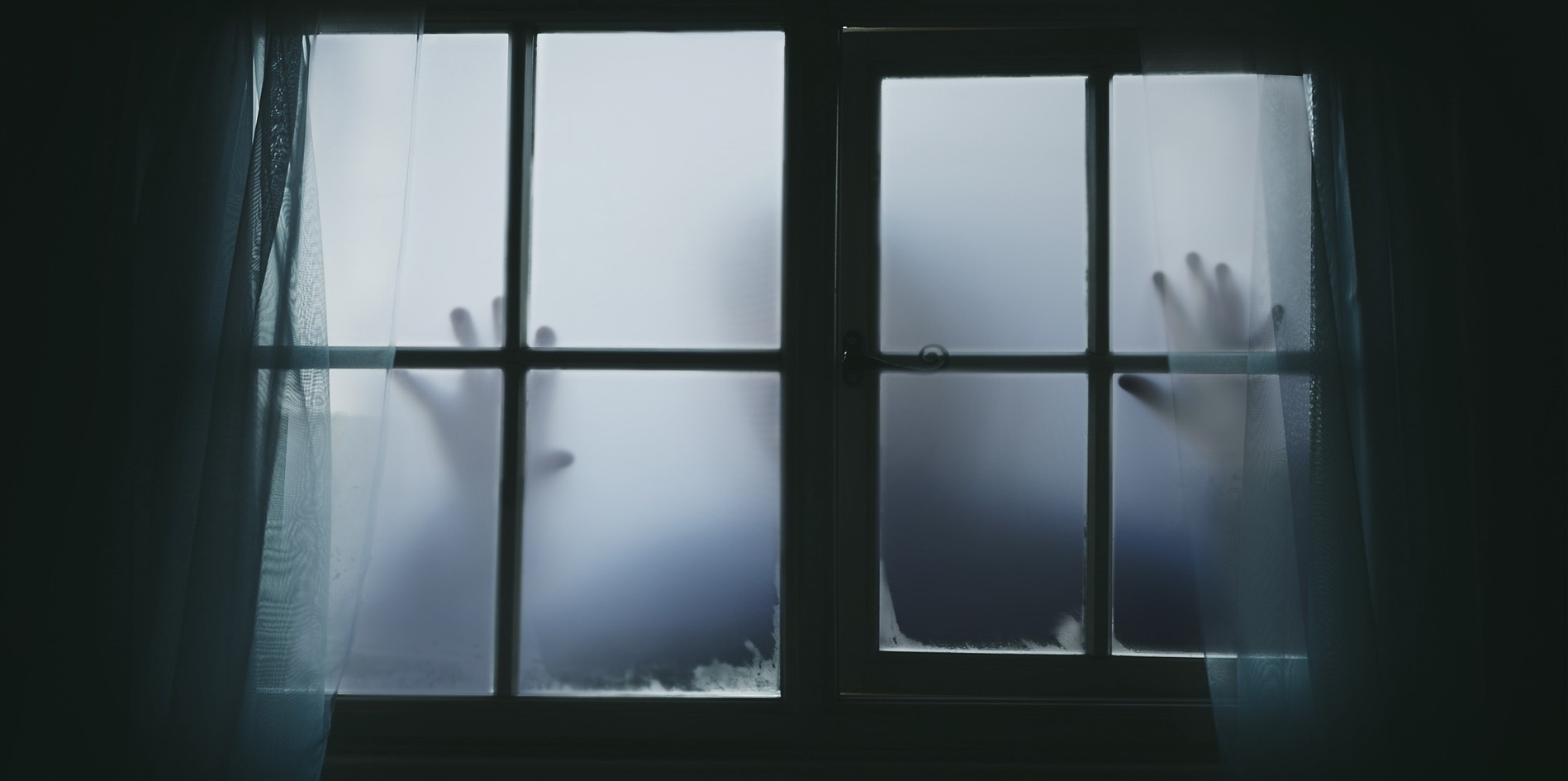
In October, our thoughts turn to all things spooky. Whether it’s scary stories, haunted houses, or dressing up like monsters, this is the time for fun scares! One thing that should really scare you? Outdated, end-of-life software haunting your computer or network.
When software is no longer supported, it’s not merely useless; keeping outdated software on your computer is dangerous. When companies stop releasing security patches and end support for a product, hackers jump at the opportunity to target these unpatched vulnerabilities and steal, expose, or hold data for ransom. The vulnerabilities that outdated and end-of-life software expose are low hanging fruit for bad cyber actors.
All too often, the price of a data breach is much costlier than simply investing in updated software. A well-placed cyberattack targeted at the weaknesses in your organization’s network can instigate a data breach and cause great financial and reputational damage.
Healthcare organizations, for example, often make extensive use of legacy systems and still rely on devices that have reached their end-of-life, or that are no longer supported. This makes them vulnerable to cyberattacks on their network, which can cause patient records to be exposed and private company data to be released. Research consistently shows that healthcare data breach costs are among the highest across industries, showing an urgent need for the best cybersecurity practices.
Outdated software can play a role in supply chain cybersecurity as well. If lower-tier suppliers are using end-of-life software, it can expose the entire supply chain to vulnerabilities, and the damage from an attack can touch every member. In the case of manufacturing supply chains, outdated software could also lead to compromised parts or other hardware that create problems in the finished product. Vendors who supply software to any member of your supply chain should ensure they have planned for how they will handle legacy support for end-of-life products. If you’re building something new based on a vendor’s software, be sure to ask about the product’s lifecycle and what it will mean for you when the product or version of the product you’re using reaches the end of its life.
All good things must come to an end—but often there’s something better on the other side! From improved functionality to new features, up-to-date software is all treat and no trick.
Don’t let end-of-life software haunt your computer. Stay a step ahead.
CDN Supply Chain, powered by Celerium, is a next-generation solution that empowers industrial enterprise organizations to improve the cyber defense posture of their suppliers and critical partners. Through both informational solutions and best of breed cyber threat sharing, CDN Supply Chain can help you secure your supply chain from your largest top-tier supplier to your smallest lower-tier supplier. Contact us today to learn more!